Know the Unknowns – Cyber Security Today
By Alexander Kaufman | CISSP, CISA, GSTRT, GSNA Back in 2002, Donald Rumsfeld, the US Secretary of Defense, broke down threats into three categories of “knowability”:
- Known knowns – those are the things we know that we know;
- Known unknowns – those are the things we know we don’t know;
- Unknown unknown – this category includes the things we don’t know we don’t know.
While Mr. Rumsfeld’s speech was focused on US national security, his categorization can be easily applied to cybersecurity in general, and to cybersecurity risk management in specific. It is not a secret it is much easier to design and implement security controls that provide a level of protection against known threats. Not only are these controls required by different regulations, it also looks good on the paper when you apply them. This is why most of Information Security leaders are choosing to focus most of their efforts and resources on the
known knowns, instead of trying to understand what are the hidden risks that the organization is exposed to, and what are the things that they don’t know yet – the
unknown unknowns. In today’s world where cybercriminals have capabilities like never before, this approach of “
First, let’s fix what we know and then will start thinking about what we don’t know” can lead the organization to disaster. The organization must operate in a more proactive manner to identify and understand the impact of hidden risks. New cybersecurity activities must be integrated with already existing processes to make the security operation fast, continuous, and efficient. This is the time when business executives must take off their rose-colored glasses, stop being passive when enjoying nice CISO’s presentations, and start asking the right questions. Because if we want to protect the organization against the unknown threats, we have to shine a light on them and make them known. It is important to keep in mind that this is not a one-time thing. It is a continuous process that must be embraced by each organization. New operational practices of challenging, measuring and optimizing information security systems should be designed, adjusted and implemented. The purpose of this continuous process is to uncover new security risks and to find out if the current level of protection provides an adequate response. As a result, this process reduces an organization’s potential attack risk by constantly optimizing the security posture. To be practical, I’d like to provide some highlights to help articulate the
main ideas behind knowing the unknowns:
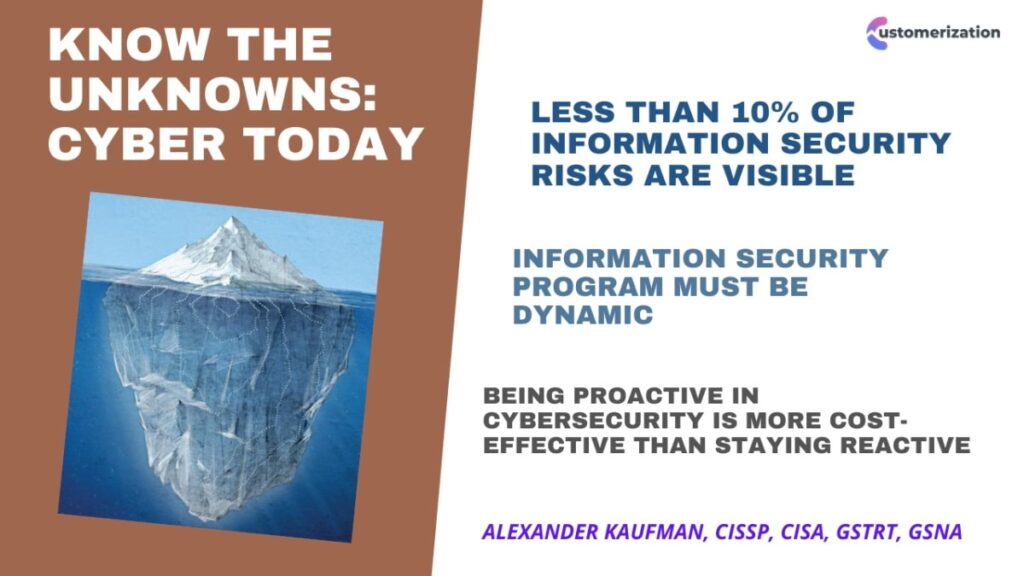
- Leaders be aware that information security risks are like an iceberg – less than 10 per cent are visible, and the rest are under the surface;
- There is no such thing as a long-term Information Security Program. A Security program must be dynamic and provide appropriate responses to existing cyber threats;
- Organizations must adopt a proactive information security approach to reveal the risks that lurk under the surface. Being proactive in cybersecurity is more cost-effective than staying reactive;
- New practices and continuous security testing must be developed and implemented to optimize the effectiveness of security controls, and to provide an adequate response to security gaps;
- The “Let’s fix what we know first” approach will never work. This is a never-ending process of fixing known gaps, which will go on forever. In order to make it more effective, organizations must adopt more comprehensive approaches to identify the unknowns and turn them into knowns.